MIT KERBEROS – DNS DISCOVERY
Description
Kerberos V introduced support for a new mechanism for locating services through DNS. It makes use of DNS resource record type: SRV (RFC-2782). Note, however, that if it is set up for the discovery of Kerberos services, but /etc/krb5.conf also contains information about where to find one or more KDCs, then the local settings will be preferred and no DNS queries will be made. At last but not least please note that the admin_server entry must be in the krb5.conf realm information in order to contact kadmind, because the DNS implementation for kadmin is still incomplete.
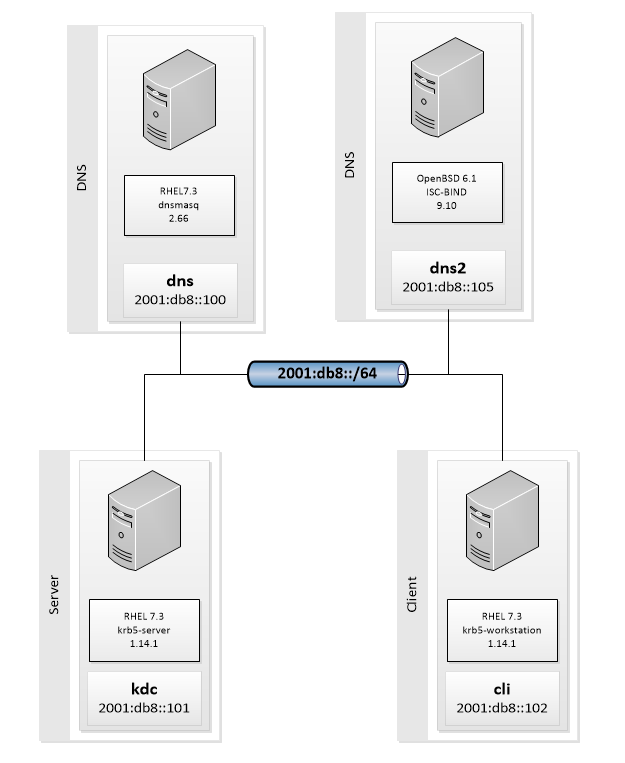
Lab Schema
Preconfiguration
Another configuration must be prepared before you will continue. Click button on the right to jump into
MIT KERBEROS INSTALLATION HOWTO (1-8)
Configs
CentOS + dnsmasq
OpenBSD + bind
1. Install dnsmasq package
[radmin@dns~]$ sudo yum install dnsmasq
---> Package dnsmasq.x86_64 0:2.66-21.el7 will be installed
--> Finished Dependency Resolution
Installing:
dnsmasq x86_64 2.66-21.el7 local 229 k
Installing : dnsmasq-2.66-21.el7.x86_64 1/1
Verifying : dnsmasq-2.66-21.el7.x86_64 1/1
Installed:
dnsmasq.x86_64 0:2.66-21.el7
Complete!
[radmin@dns ~]$
1. Install isc-bind package
[radmin@dns2 ~]$ sudo pkg_add isc-bind
quirks-2.304 signed on 2017-04-02T15:01:33Z
Ambiguous: choose package for isc-bind
a 0: <None>
1: isc-bind-9.10.4pl6
2: isc-bind-9.10.4pl6-geoip
3: isc-bind-9.10.4pl6-no_ssl
Your choice: 1
isc-bind-9.10.4pl6: ok
The following new rcscripts were installed: /etc/rc.d/isc_named
See rcctl(8) for details.
[radmin@dns2 ~]$
2. Modify hosts file
[radmin@dns ~]$ cat /etc/hosts
127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4
::1 localhost localhost.localdomain localhost6 localhost6.localdomain6
2001:db8::100 dns dns.radkowski.pro
2001:db8::101 kdc kdc.radkowski.pro
2001:db8::102 cli cli.radkowski.pro
2. Edit /var/named/etc/named.conf file and add following zone definition at the end:
zone "radkowski.pro" {
type master;
file "master/radkowski.pro";
};
3. Create dnsmasq config file
[radmin@dns ~]$ sudo cat /etc/dnsmasq.d/kerberos.conf
local=/radkowski.pro/
domain=radkowski.pro
txt-record=_kerberos.radkowski.pro,"RADKOWSKI.PRO"
srv-host=_kerberos._udp,kdc.radkowski.pro,88
srv-host=_kerberos-master._udp,kdc.radkowski.pro,88
srv-host=_kerberos-adm._tcp,kdc.radkowski.pro,749
srv-host=_kpasswd._udp,kdc.radkowski.pro,464
[radmin@dns ~]$ sudo systemctl restart dnsmasq
3. Create zone file
[radmin@dns2 ~]$ sudo vim /var/named/master/radkowski.pro
; OpenBSD: localhost,v 1.1 2014/08/22 20:32:13 sthen Exp
ORIGIN radkowski.pro.TTL 6h
@ IN SOA radkowski.pro. root.radkowski.pro. (
1 ; serial
1h ; refresh
30m ; retry
7d ; expiration
1h ) ; minimum
IN NS dns.radkowski.pro.
IN NS dns2.radkowski.pro.
dns IN AAAA 2001:db8::100
dns2 IN AAAA 2001:db8::105
kdc IN AAAA 2001:db8::101
cli IN AAAA 2001:db8::102
_kerberos IN TXT "RADKOWSKI.PRO"
_kerberos._udp IN SRV 10 0 88 kdc
_kerberos._udp IN SRV 20 0 88 kdc
_kerberos-master._udp IN SRV 0 0 88 kdc
_kerberos-adm._tcp IN SRV 0 0 749 kdc
_kpasswd._udp IN SRV 0 0 464 kdc
[radmin@dns2 ~]$ sudo rcctl restart isc_named
4. Check DNS config
[radmin@cli ~]$ dig -t txt _kerberos.radkowski.pro
; <<>> DiG 9.9.4-RedHat-9.9.4-37.el7 <<>> -t txt _kerberos.radkowski.pro
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 12643
;; flags: qr aa rd ra ad; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;_kerberos.radkowski.pro. IN TXT
;; ANSWER SECTION:
_kerberos.radkowski.pro. 0 IN TXT "RADKOWSKI.PRO"
;; Query time: 0 msec
;; SERVER: 2001:db8::100#53(2001:db8::100)
;; WHEN: Tue Jul 11 23:55:26 BST 2017
;; MSG SIZE rcvd: 67
[radmin@cli ~]$
4. Check DNS config
[radmin@cli ~]$ dig -t txt _kerberos.radkowski.pro
; <<>> DiG 9.9.4-RedHat-9.9.4-37.el7 <<>> -t txt _kerberos.radkowski.pro
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 19110
;; flags: qr aa rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 2, ADDITIONAL: 3
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 4096
;; QUESTION SECTION:
;_kerberos.radkowski.pro. IN TXT
;; ANSWER SECTION:
_kerberos.radkowski.pro. 21600 IN TXT "RADKOWSKI.PRO"
;; AUTHORITY SECTION:
radkowski.pro. 21600 IN NS dns.radkowski.pro.
radkowski.pro. 21600 IN NS dns2.radkowski.pro.
;; ADDITIONAL SECTION:
dns.radkowski.pro. 21600 IN AAAA 2001:db8::100
dns2.radkowski.pro. 21600 IN AAAA 2001:db8::105
;; Query time: 0 msec
;; SERVER: 2001:db8::105#53(2001:db8::105)
;; WHEN: Wed Jul 12 22:37:46 BST 2017
;; MSG SIZE rcvd: 171
[radmin@cli ~]$
Client Config
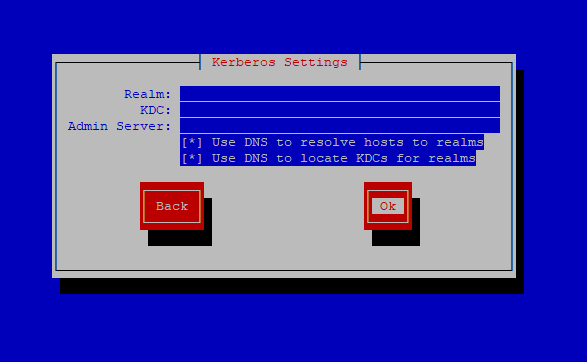
5. Reconfigure system authentication resources
[radmin@cli ~]$ sudo authconfig-tui
Test Area
6. Test configuration
[radmin@cli ~]$ klist
klist: Credentials cache keyring 'persistent:1000:1000' not found
[radmin@cli ~]$ kinit
Password for radmin@RADKOWSKI.PRO:
[radmin@cli ~]$ klist
Ticket cache: KEYRING:persistent:1000:1000
Default principal: radmin@RADKOWSKI.PRO
Valid starting Expires Service principal
11/07/17 23:38:47 12/07/17 23:38:47 krbtgt/RADKOWSKI.PRO@RADKOWSKI.PRO
[radmin@cli ~]$
